Elon Musk Blames ‘Massive Cyberattack’ for Widespread X Outage – March 10th
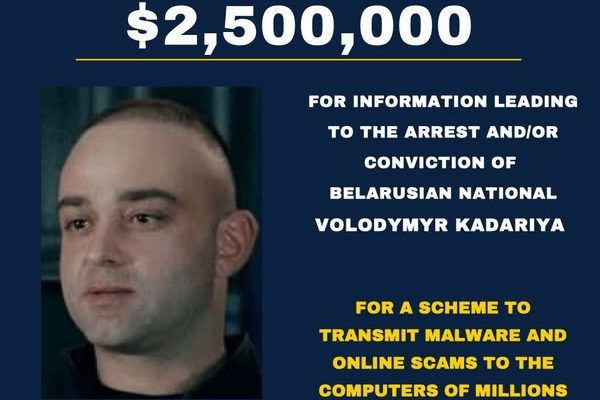
Social media platform X suffered a major outage on March 10, with tens of thousands of users unable to access the site. Owner Elon Musk blamed the disruption on a “massive cyberattack,” suggesting that a well-funded group or nation-state may have been involved.
The outage, which peaked around 10 a.m. EST, affected both the X app and website, with intermittent service disruptions continuing throughout the day. As frustrated users flocked to alternative platforms like Threads and Bluesky, concerns grew over the security of X’s infrastructure.